This question it the basic of the web challenge if we go to the link given above we usually get a message like this when we visit the page for the first time 🙂
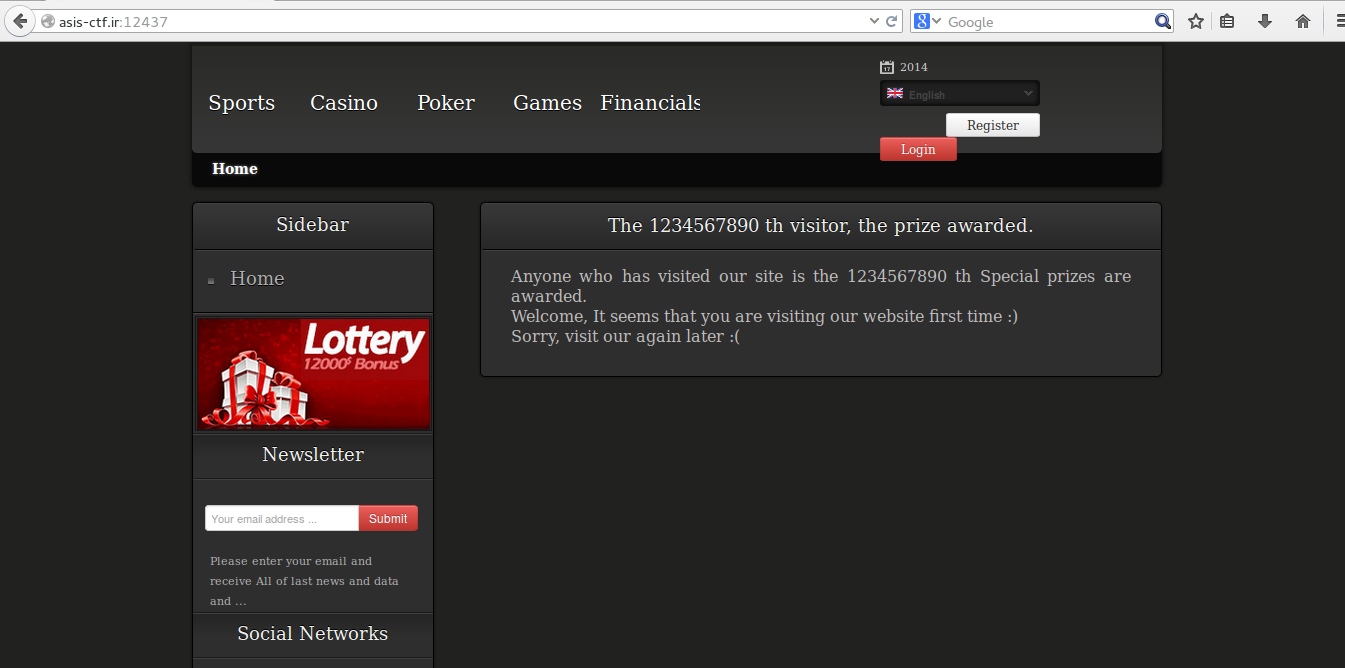
As the page says let’s visit the page for the second time 🙂
So here comes the lottery which says that we are 2444th visitor and we need to become the 1234567890th visitor to get the lottery also with the clue saying that don’t hack cookies. We should be always doing the thing that we are not supposed to do so let’s try hacking the cookies. But the first thing we need to do when we see a web question is to view the source page of the given question 🙂 but when you see the source page you will understand that there is no other way to find the visitor number except the cookie 🙂
If you not aware what a cookie is find about it http://en.wikipedia.org/wiki/HTTP_cookie
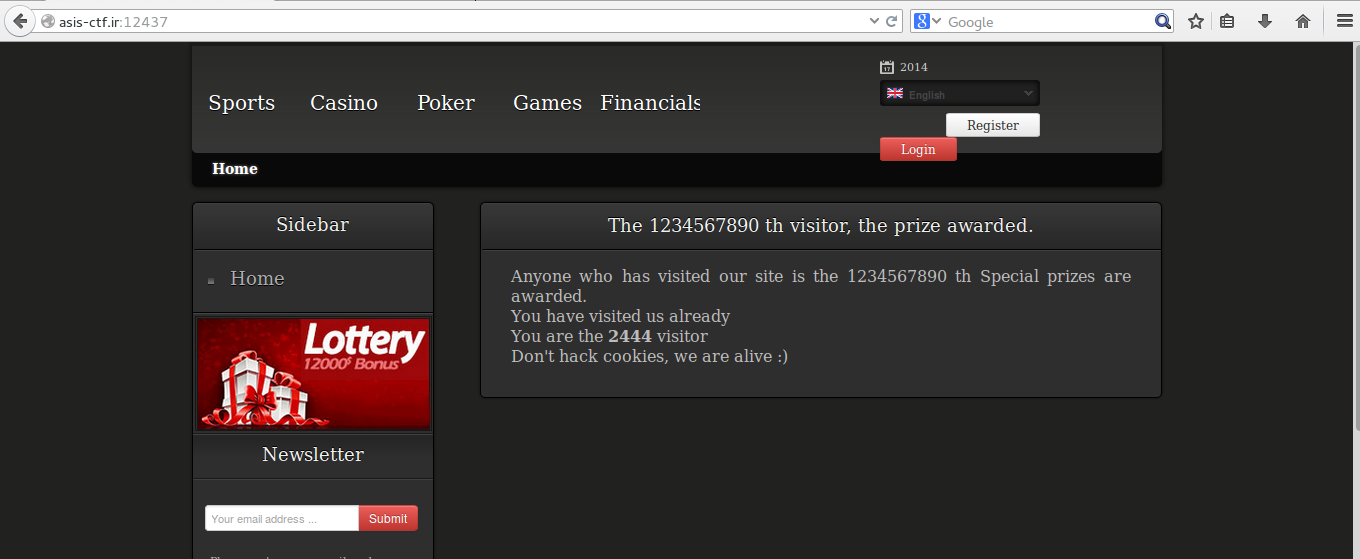
I have a cool tool which is called as “edit this cookie” to edit the cookies you can get it in the chrome store at https://chrome.google.com/webstore/detail/editthiscookie/fngmhnnpilhplaeedifhccceomclgfbg?hl=en
if you look at the cookie named Visitor you will see a value like this which is url encoded
MjQ1Njo3Y2Y2NDM3OWViNmYyOWE0ZDI1YzRiNmEyZGY3MTNlNA%3D%3D
for more details about it visit this wiki page of the URL encoding http://en.wikipedia.org/wiki/Percent-encoding
If you have doubt why we should use the URL encoding this link will give the answer to you http://stackoverflow.com/questions/4667942/why-should-i-use-urlencode
If you decode it using any tool, I use this online tool http://www.url-encode-decode.com/
The decoded result will be like this
MjQ1Njo3Y2Y2NDM3OWViNmYyOWE0ZDI1YzRiNmEyZGY3MTNlNA==
which again seems to be like a base64 encoding if you decode it the output looks like this
2456:7cf64379eb6f29a4d25c4b6a2df713e4
2456 seems our number which we visited so if we could change the number to 1234567890 we could win the lottery (get the flag 😀 )
The number after the 2456 is nothing but the md5sum of the number 2456 🙂
so
1234567890:e807f1fcf82d132f9bb018ca6738a19f
is the one we need to make the value of the cookie to base64
MTIzNDU2Nzg5MDplODA3ZjFmY2Y4MmQxMzJmOWJiMDE4Y2E2NzM4YTE5Zg==
and finally we need to encode it with URL encoding which looks like
MTIzNDU2Nzg5MDplODA3ZjFmY2Y4MmQxMzJmOWJiMDE4Y2E2NzM4YTE5Zg%3D%3D
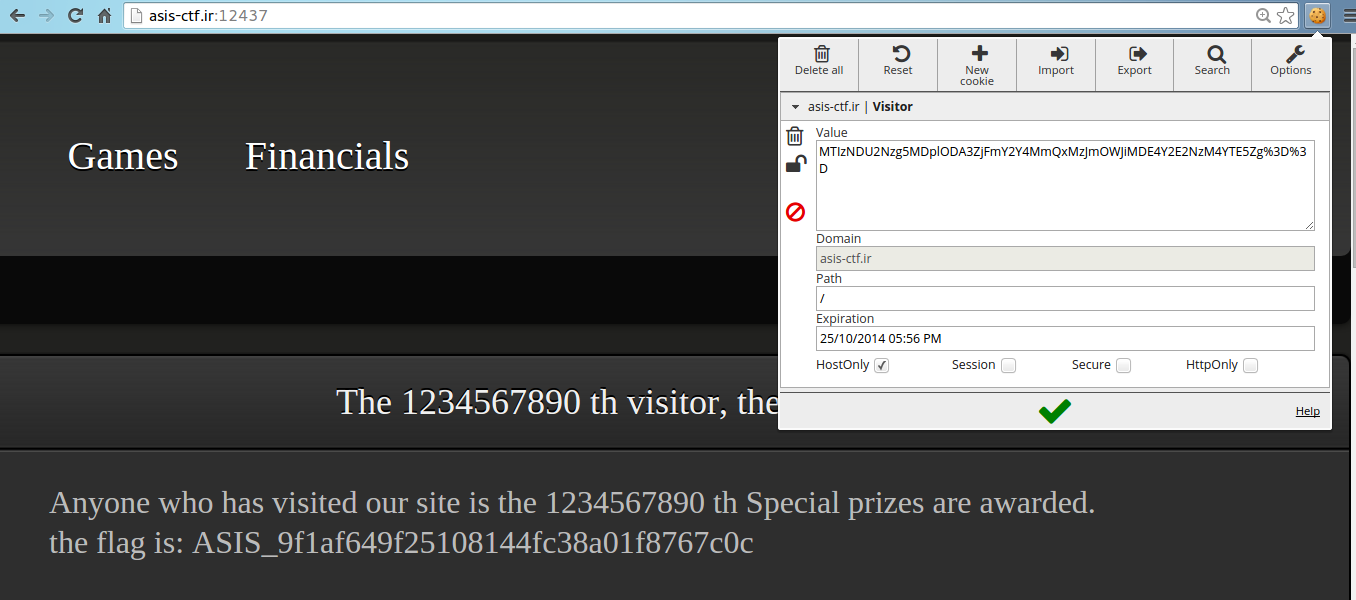
so if you submit the cookie and refresh the page you get the flag as
ASIS_9f1af649f25108144fc38a01f8767c0c
Here is the screenshot of the flag 🙂