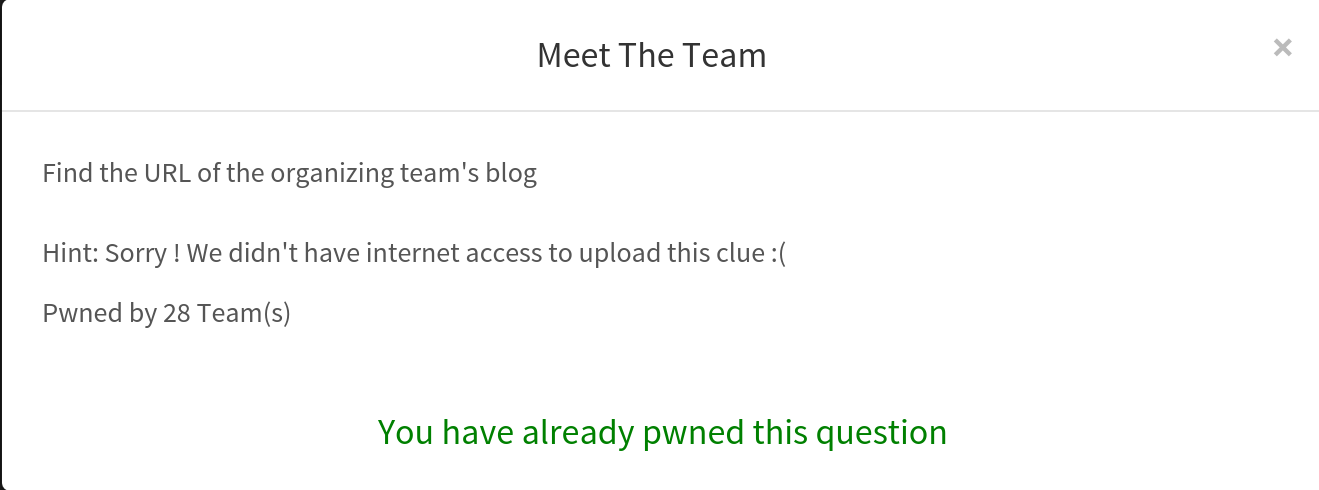
I have attached the screen-shot of the question 🙂 of Recon-80
The question is very simple but getting the blog of the team becomes hard because ECTF is organised for the first time.
The ECTF organizers doesn’t have a good blog which contains all the write up’s that they have solved, it seems like they have created blog just for the case of the challenge as the blog contains only one post which makes it difficult for the search engines to get the get that link (if any of you googled for the blog and did not get the link don’t blame google as it is doing a great job)
The name of team which is organising the ctf is NIA (no internet access). They have mentioned it in the clue also but you will never get to know that it is the name of the team for more details visit this link http://nia-ctf.github.io/
Bingo you got the blog link in the ctftime.org at this address https://ctftime.org/team/8096 and you get the link as http://nia-ctf.github.io/ so you got the flag, there was some small confusion regarding the format of the flag but the admin would have helped you at that time 🙂