Hello every one 😀
In this post I will be sharing my experiences on InCTF2015, I am writing this blog as the admins of the CTF have made it a question worth of 100 and the difference between us and the next team below us was just a matter of solving the question first (bonus score) any way I don’t think that there will be any bonus score for this question as I am not the first one to send my experiences and hope the VYkingS team didn’t send the experience first 😛
And also I wish that the awarding points will not be done as in the collage exams (based on the length of the answer written lol :P). One more thing this is not just my personal experiences, these represent the team (beginners) experiences (another way of saying other members in the team may or many not write their own :D, best way to skip the job)
Enough of this intro, to be frank InCTF is the only challenge which made me feel confident that, I can achieve something great 😀 words are not sufficient for me to describe about this CTF and I am not a writer too 😛 (doesn’t mean that this is the end of the post)
I have taken part in some ctf’s like PicoCTF but I have never participated in the live ctf and able to solve this many challenges and had a real feel of CTF and competition and thinking to win it and really won it 😀
So I will say how this ctf went on, first of all the day before the challenge I was given the task to submit the first round tasks by sending them a email. I was having holiday on friday as there were some cultural events so I slept a lot on the friday and in the night I started looking at the first round question and trying to complete them if there were any blanks and some missing things etc.. So I submitted them around 5 AM (as usual do the assignment on the last day in engineering :P). My team mate told that he will wake me up at 9 AM and thought to get ready by 10AM and start the competition. Thank God that on the friday something big happened in the Kerala and Saturday was declared as hartal (bund – In kerala you can expect them once in a week so lot of holidays for our college 😛 )
My friend Rakesh (rok_ in IRC) woke me up only at 10AM so that I can more sleep 😀 and then came to known that the ctf will be starting only at 12, I felt very happy as I need not start the ctf lately (as in the case of normal class and then ask faculty for attendance and attendance is very strict in Amrita :P) This definitely helps us as other wish we couldn’t have scored the bonus points which made the lead the CTF. So saw the India batting for some time and the wickets fell continuously so I stopped watching (you know these lucky things right :D) And then I started going to lab knowing everything regarding harthal is fine now (as the wifi at the hostel sucks as less as 50kbs which is far less than the 3g speed in my mobile)
Sai Ram (blah_blah) was already there in the lab waiting for the challenges to come online (he is our crypto expert) after that we had our food in mess (mess food really sucks here 🙁 ) and then our other members Rakesh and Abhishek(REVO in IRC) joined us.
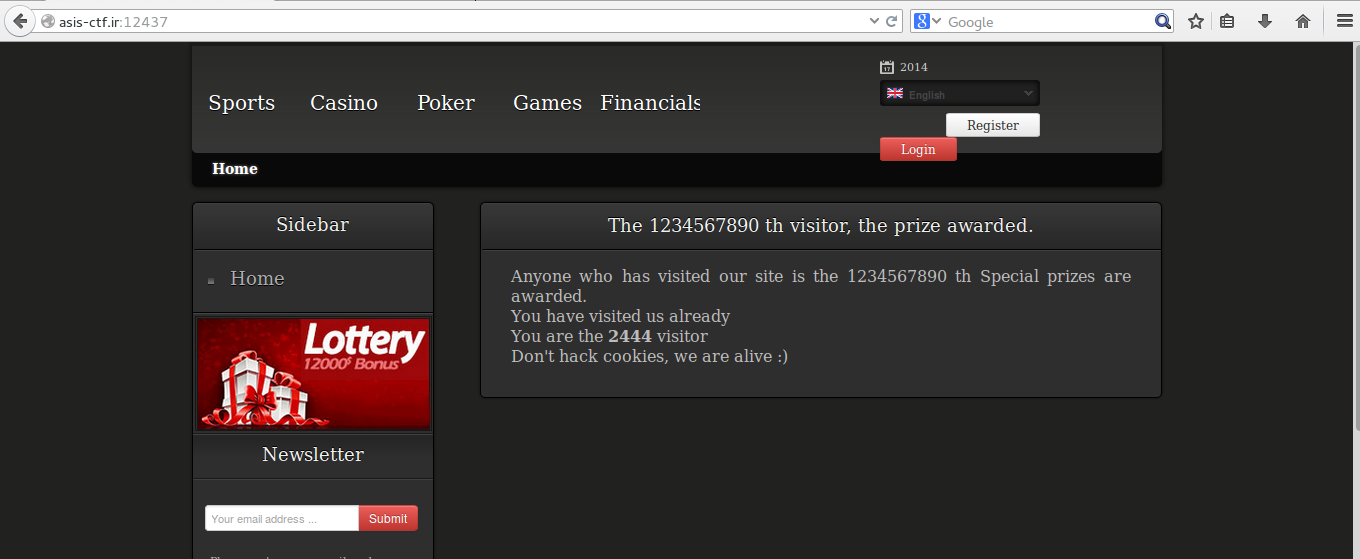
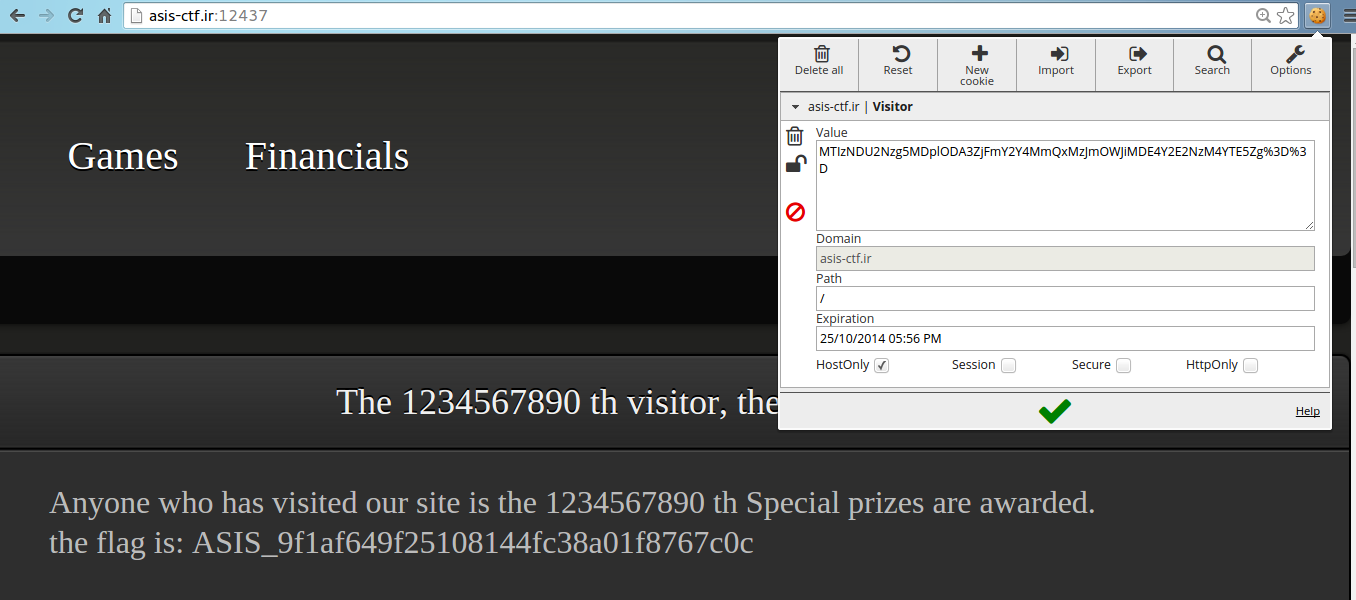
So in this manner all the ctf started and the first thing that we targeted was triva as it’s the best way was to score the points easily. So we got hefty points (including bonus points) in the starting and we solved all the triva(including twitter picture the top image in the blog) except 2 question the ip one and the docx one.
I tried for the ip one as localhost as I know nothing more than that as I haven’t taken my network classes yet, then later I asked the same with admin, he told I was correct but there was some similar name to the localhost and always I found was loopback and then I gave a try with it and got the flag
We we stuck at the docx one till next day It was my mistake 🙁 after extracting the tar.gz file I got a zip file, instead of a second thought I just unzipped the file 🙁 this was my dam mistake and I was getting the answer by zipping the file again and renaming the file to docx and this didn’t work because the version of the zip in my machine was a latest one 🙁 , When the admins told that they have told that they have made the question easy for us, I got the flag in matter of just typing 😀 , Lesson learned if you are not getting a simple challenge try to start doing it again you might have done something wrong
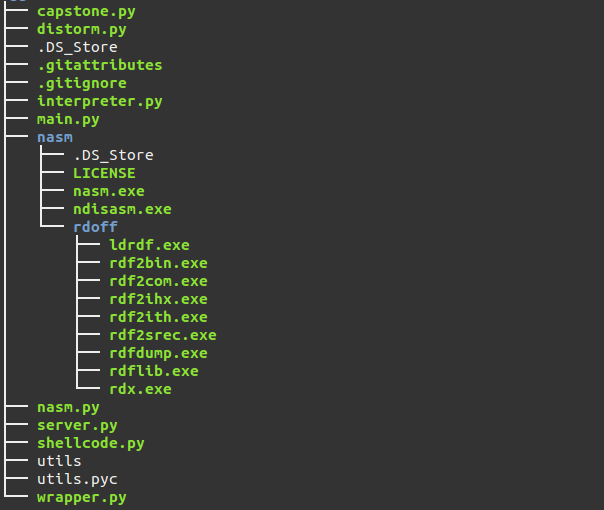
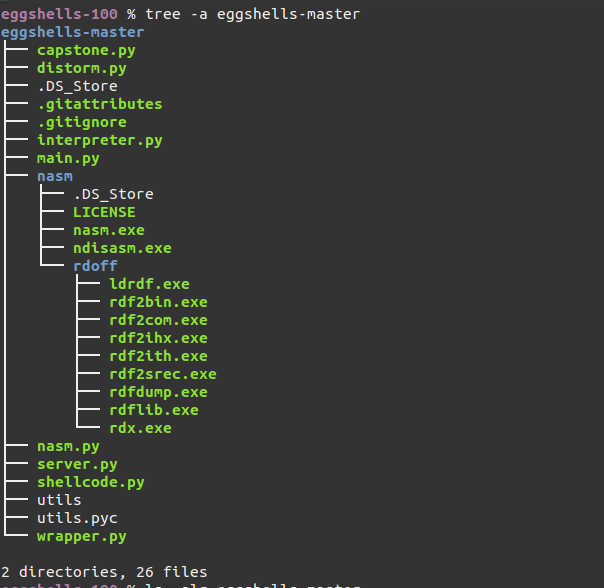
My area is RE so I first about those problems, The first two sums were pretty easy and I got them as soon as opening them in the IDA pro. first one was a small ARM question and second one was hardcoded password strings will give the flag
And the third one was jar file, I have jad (java decompiler no need online one :D) and then decompiled them but I have never coded in java and all the problems I have done in picoctf were just hard coded ie the password was right there when I just decompiled them So I have postponed this one to next day ( I should have done it now it self as it was also very easy one)
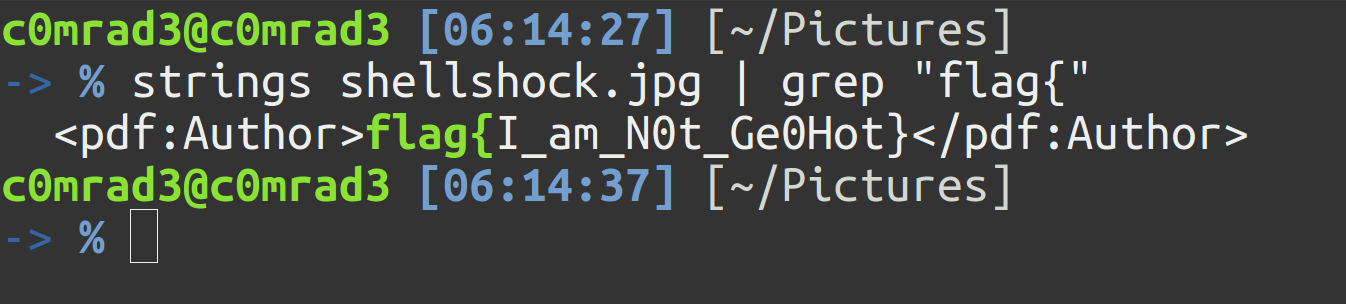
I started doing the Forensics even thought, It was not a my piece of cake, the first one which I solve was fixme one in this question we were given a image file and It was damaged, as per my knowledge the thing that they would have done is just changed the header of the image, but I have never used any tools or hexedit to change it to match the exact header, but the online services have saved me from a lot of googling and installing new software 😛 and got the image fixed not sure which one worked for me but I will mention them in the write-up if I have time
Second one was pcap file and my friends found something interesting in the wireshark which say it’s the key (but it didn’t say that it is the flag :P) we have submitted many times the same key and even told admins that the question has some issue with it, later we came to know that we need to get a file from the pcap and this is the key to open the file. I have used a lot of tools in windows vm to get the files from the pcap file but nothing worked well (or my vm is bad) but I found a ausome tool for linux named foremost which gave me the zipped file in a matter of seconds and I used the key to unzip the flag and then got the flag 😀
I have tried many other sums but not sure if i can explain them here, few of the web question were solved by Abhishek (REVO) one was 9999 sum we need to give the hex value not sure about the second one
Rakesh (rok) was able to solve few binary not sure how he got them
By the night around 12 we got the score of 1500 and we have been in almost top 5 (not sure about it it might be top 10 too) so we did our best for the first day
So I and rakesh decided to take good rest so that we will be able to solve theres well tomorrow and Sai ram and abhishek decided to burn the midnight oil 😀
In the night on return we had a great opportunity to steal mangoes from one house on our way back to hostel (every day there used to be a dog and it was our lucky day that it wasn’t there or sleeping) we ate the first mango of this season even before ugadi (ugadi is festival of Andhra people)
And the best part was the hostel door was locked and only way we can enter is by jumping the wall (which is common for us don’t say it to our warden)
Next day I was in the lab by 9 AM (every one was surprised as I never got up that early on sundays and came to lab)
This day was not that successive in points (but we were moving close to our answers slowly) Our position went as bad as 20 but we were still first in our campus (so that we will be sure for the 3rd round)
But something worst happened to us we were overtaken by a girls(seniors) team from our campus who are participating in the ctf for the first time (no offence anonymous I suggest you choose a another team name as this name doesn’t have a good name in the security field)
But the lesson learned was never give up even thought every thing seems very difficult (as we can say from our results as we topped)
But when the hints were given we were able to slowly get the score in the ending and the mass hints very useful to us 😀
We will be trying to write writeups and explaining them very clearly and updating this post too
Any way we were able to solve all the RE and crypto (credits goes to Sai ram our crypto master re all except which were taken down)
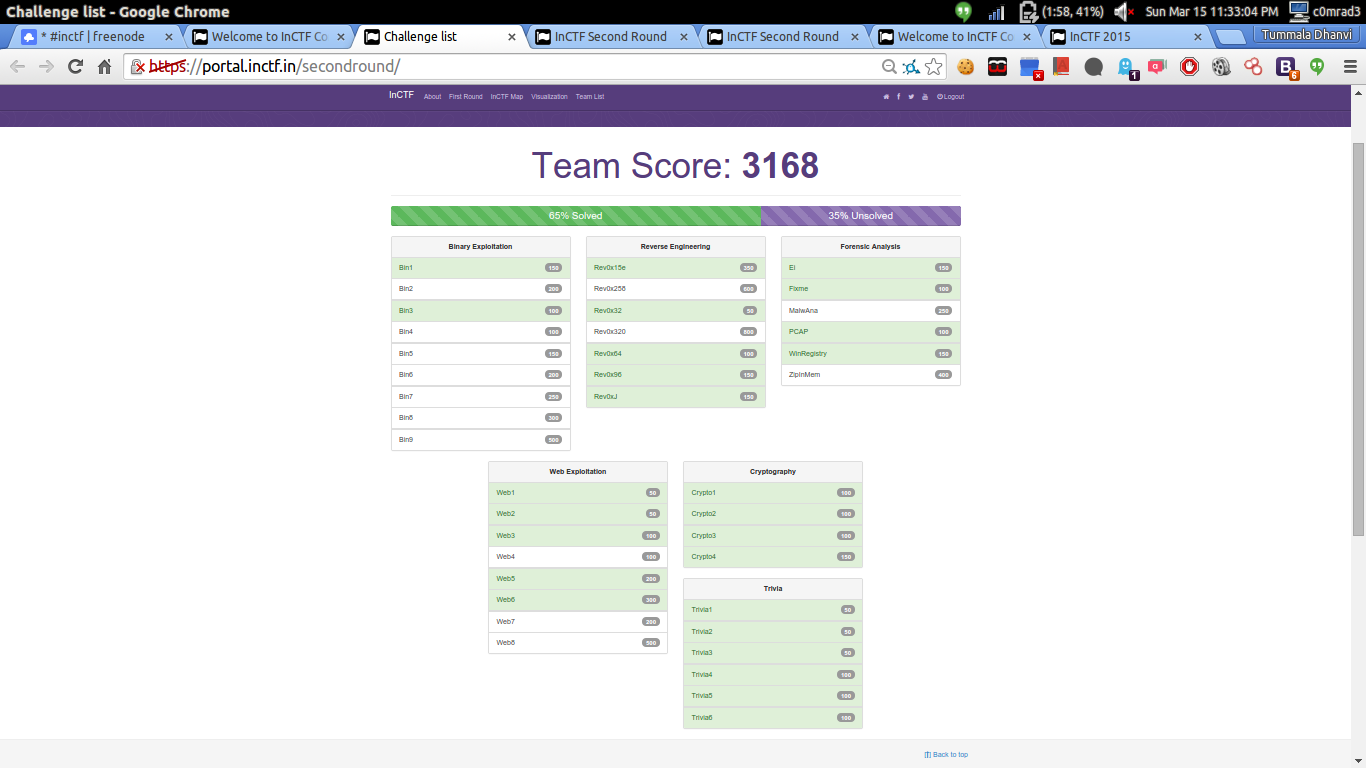
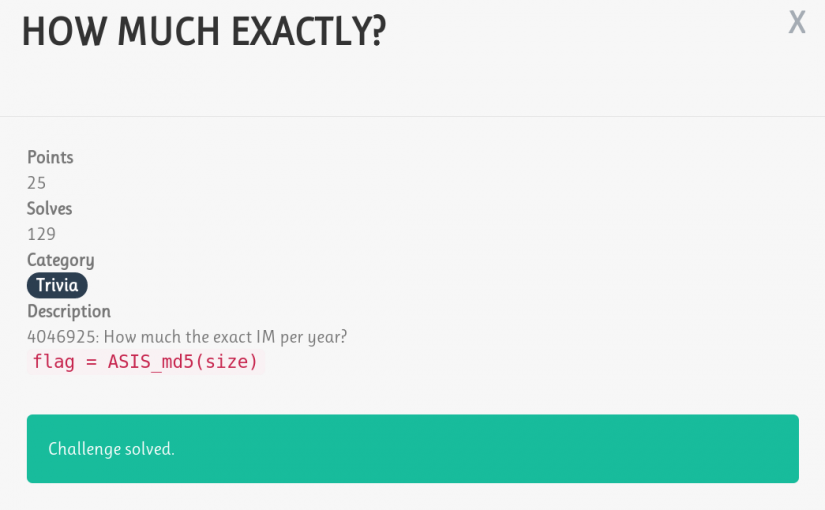
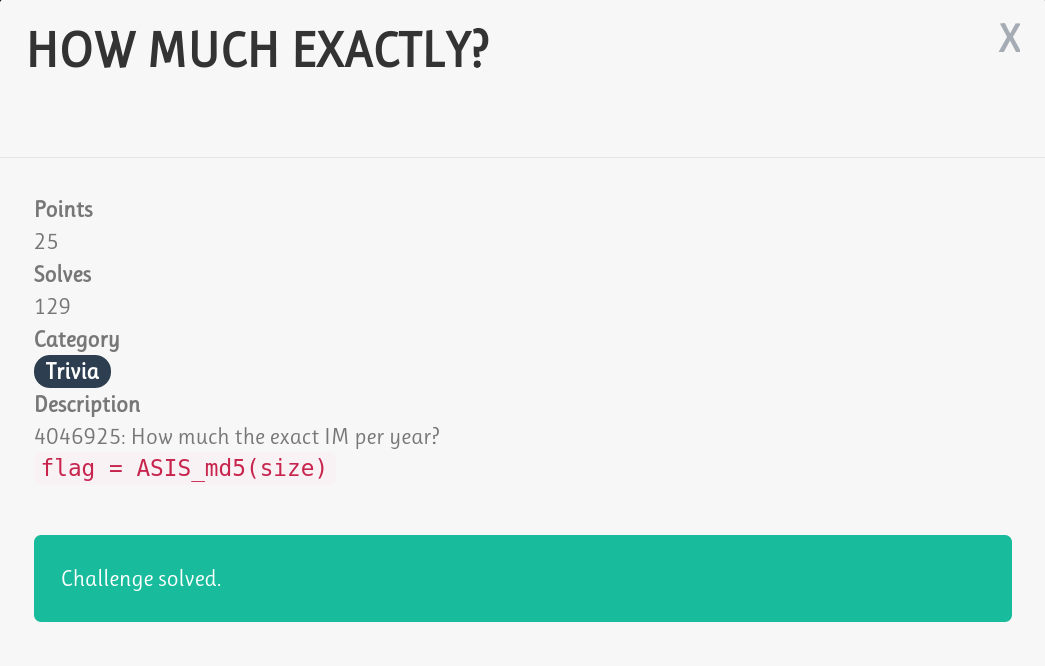
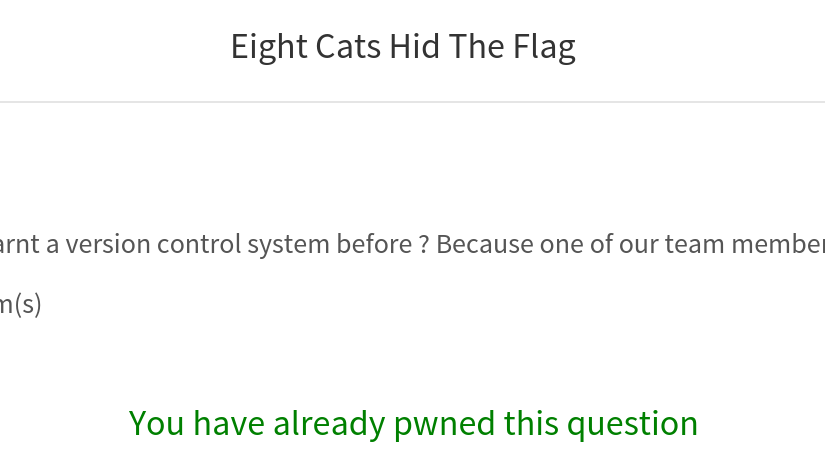
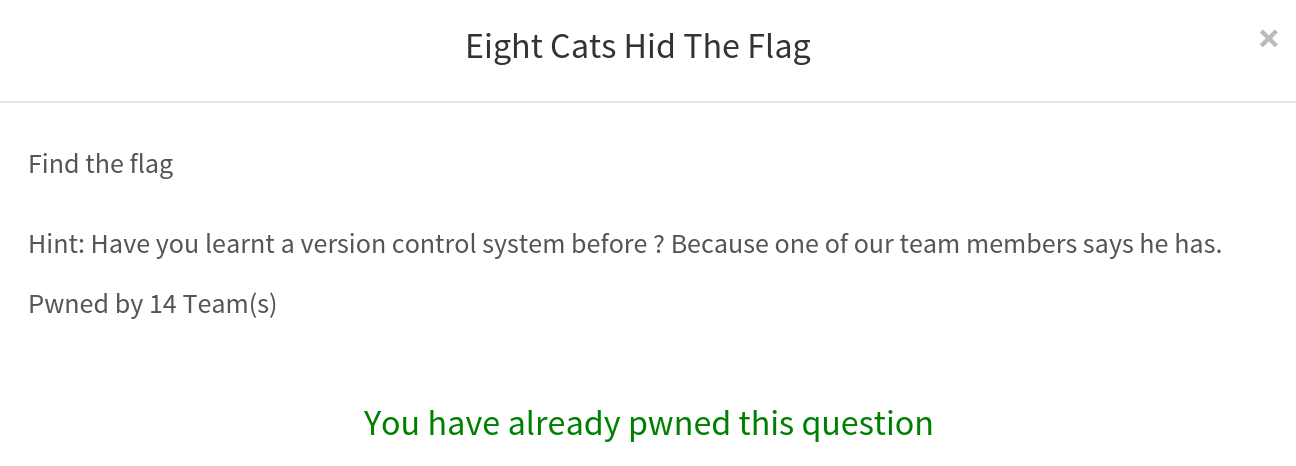
here is the screen shot of the question solved In the last minute our target was just to make sure that our team will be first, the new opponent that we have is the IITR VKingS team which came equal to us (except for the bonus points) all our team members are working in the last minute to make sure that we score one more question and remain in our position. I and sai ram were working on forensics and Rakesh binary Abhishek Poodle question (If we were able to continue solving the same we would have been no where reachable to other team)
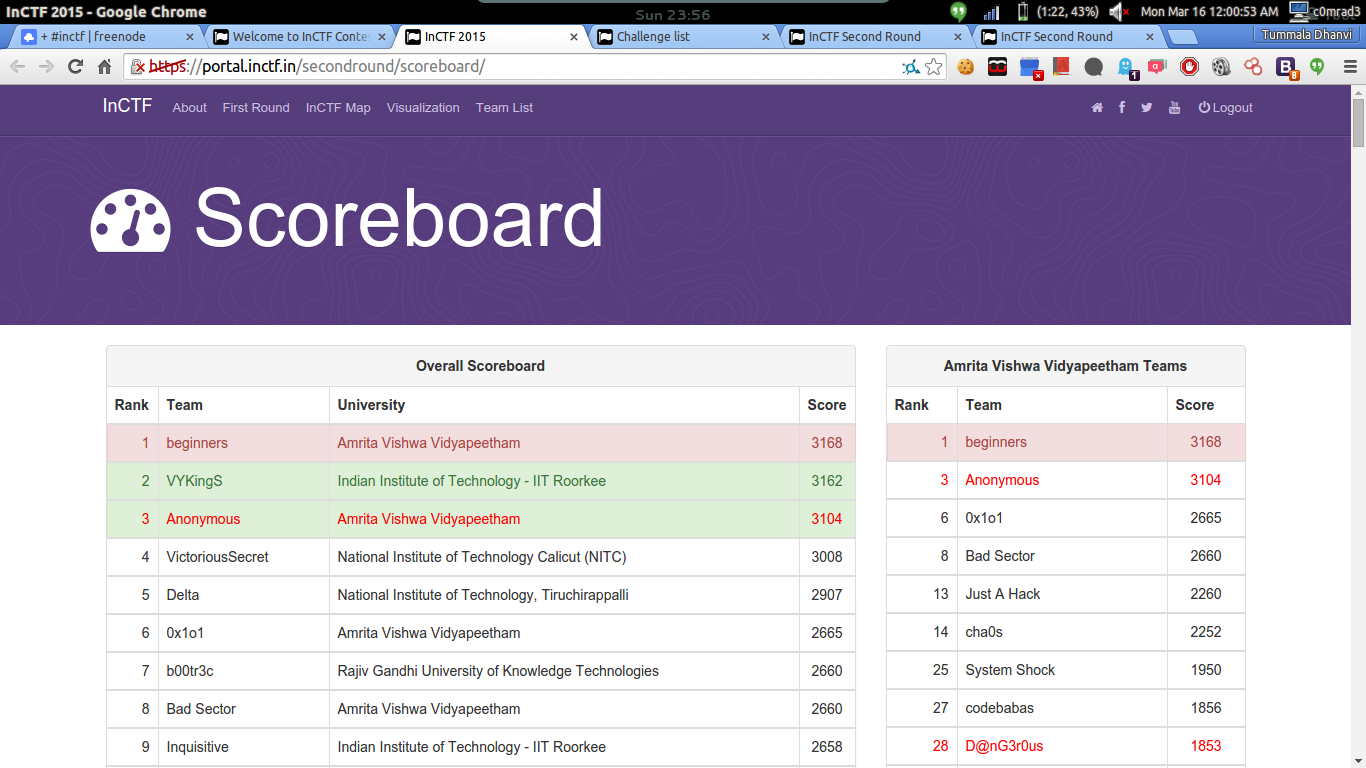
Any way the final score was like this
Now coming the final words (I have been told by admins the points for this question will be awarded based on the how well we appreciate the team and their work 😛 jk)
Over all the CTF was Excellent 😀
We appreciate all the people who are responsible for creating this great event
The greatest thing about this event is that this event was that this event was not at all run for profit and the motto of InCTF was to make more people from our country interested in Cyber Security and all the event organizers didn’t expect any thing in return other than our active participation (though they get some experience in conducting CTF’s :P)
Also Definitely InCTF2015 sponsors VMWARE definately as they are the main people sponsoring this event by bearing all the money for the servers and travel charges for the 3rd round etc … Think of the case if they weren’t there and each team has to pay 200 INR in the form of DD to Amrita University, the case would have been different
Fedora for make more girls team to participate
Mycodeschool for publicity (even though some team complain that publicity was not so good, hope they understand that the resources(money) are very less )
Not the least Amrita University Cyber Security Department (believe me I won’t get any extra credits for this 😛 )
Cons :- (Indian can complain about every thing even though every thing was perfectly good 😛 )
Rules were not clear for example the 3points bonus score I think it’s no where mentioned in the website even thought we figured it out very fastly
Also wish every question were named as in picoctf based on the question type not just bin1 bin2 so on, but clues made it clear, forensics question names were based on the type thought
Website is too old 😛 think it can go for a new design
That’s it 😀
Tummala Dhanvi (c0mrad3 black shirt in the behind main photo)
Sai Ram ( blah_blah white checks in the behind)
Abhishek (REVO man with spects red shirt selfe taker :P)
Rakesh (rok_ remaining one 😛 )